
CrowdStrike Container Security
Providing DevOps-ready breach protection for containers
CrowdStrike Container Security
Empower developers to protect containers, Kubernetes and hosts from build to run, on any cloud with CrowdStrike Container Security.
Full Lifeccle Container Protection for Cloud-Native Applications
Organizations are increasingly adopting container technology such as Docker and Kubernetes to help drive efficiency and agility. Containers have changed how applications are built, tested and utilized, enabling applications to be deployed and scaled to any environment instantly. As container adoption increases, they emerge as a new attack surface that lacks visibility and exposes organizations. Blind spots lead to silent failure and ultimately breaches. Most organizations have low container visibility for the following reasons:
- Traditional security tools are not designed to provide container visibility
- Tools such as Linux logs make it difficult to uniquely identify events generated by containers vs. those generated by the host, since visibility is limited to the host
- Containers are short-lived, making data collection and incident investigation challenging because forensic evidence is lost when a container is terminated
- Decentralized container controls limit overall visibility
Once a container is launched and running, it can be compromised. Even if the image is configured properly and verified, it is susceptible to new vulnerabilities and runtime threats. The dynamic and portable nature of containers further complicates securing them. Rapid scaling means the attack surface is constantly changing, while portability across multiple environments further limits and complicates visibility.
Manual processes and traditional solutions can’t match the rapid change and unique challenges organizations now face with containers. Alternative choices can include complex cloud security platforms or siloed tools, which can add more vendors and increased complexity to your organization’s overall security.
CrowdStrike Security that is fast and scalable
CrowdStrike Container Security automates the secure development of cloud-native applications, delivering full stack protection and compliance for containers, Kubernetes and hosts across the container lifecycle. This solution replaces outdated methods with an immutable infrastructure approach that optimizes cloud resources and ensures that applications are portable and always deployed securely. CrowdStrike Container Security comes complete with vulnerability management, continuous threat detection and response, and runtime protection, combined with compliance enforcement and automated continuous integration/continuous delivery (CI/CD) pipeline security, enabling DevOps teams to stay secure while building in the cloud.
Stopping breaches in container and Kubernetes environments using cloud-scale data and analytics requires a tightly integrated platform. Each function plays a crucial part in identifying vulnerabilities early, detecting threats, protecting at runtime and enforcing compliance. Containers are designed and built for speed, scalability and reliability.
CrowdStrike has deep experience in operating one of the largest security clouds in the world, providing unique insights into adversaries and enabling the company to deliver purpose-built solutions that defend against data breaches, create less work for security teams and optimize cloud deployments.
Key Benefits of Container Security Optimized for Devops

IDENTIFY VULNERABILITIES FROM DEVELOPMENT TO PRODUCTION FOR ANY CLOUD
Protect cloud-native applications and reduce the attack surface by detecting vulnerabilities, hidden malware, secrets/keys, compliance violations and more - from build to runtime - ensuring only compliant containers run in production.

"SHIFT-LEFT" SECURITY INTO THE CI/CD PIPELINE AND AUTOMATE DEVSECOPS
Integrate frictionless security early into the continuous integration/continuous delivery (CI/CD) pipeline, and automate protection that empowers DevSecOps to deliver production-ready applications without impacting build cycles.

PROTECT AGAINST ATTACKS WHEN CONTAINERS ARE THE MOST VULNERABLE - AT RUNTIME
Build and run applications knowing they are protected. Get access to automated discovery, runtime protection, continuous threat detection and response for cloud workloads and containers, and managed cloud threat hunting in a single platform.
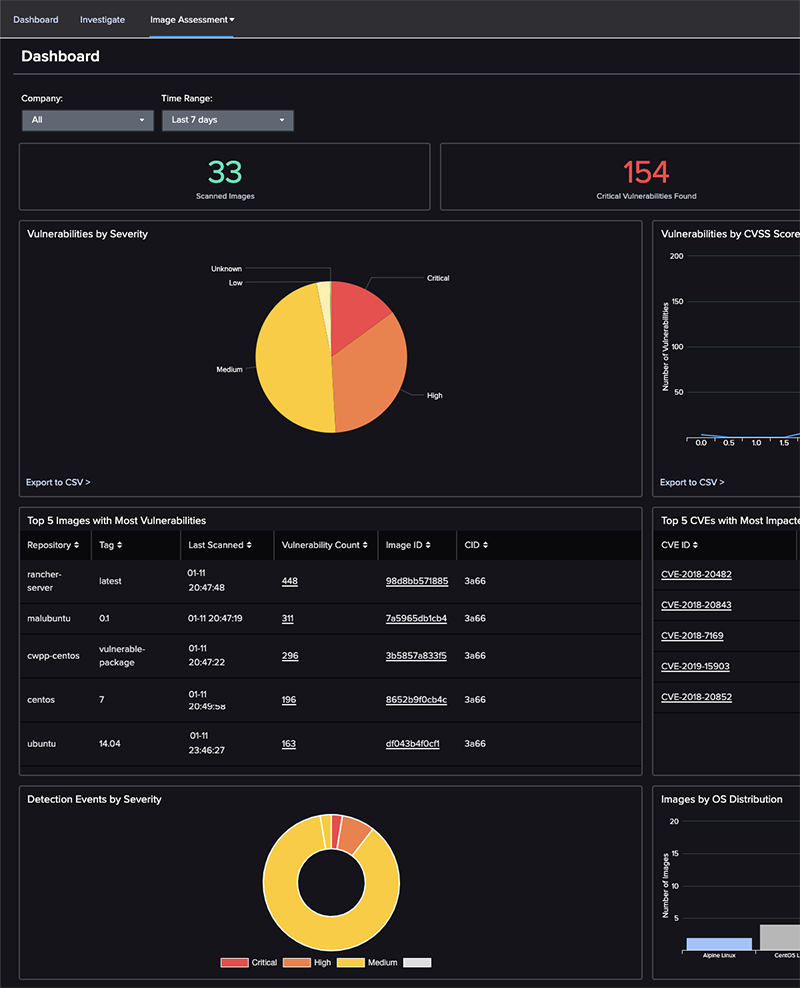
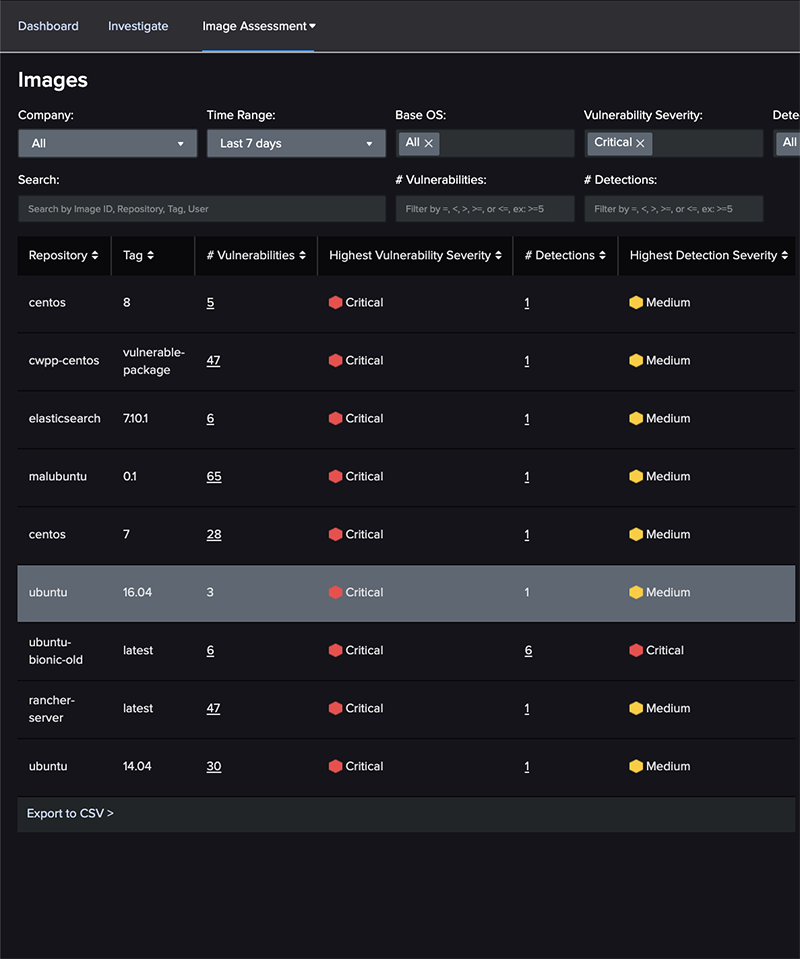
Vulnerability Scanning and Management
- Improve decision making: Gather insights and details about your cloud workload, and container - images, registries, libraries and containers spun from those images.
- Uncover hidden threats: Find hidden malware, embedded secrets, configuration issues and more in your images to help reduce the attack surface.
- Gain visibility into container environments: Get full visibility into running containers to uncover details surrounding file access, network communications and process activity.
- Identify vulnerabilities faster: Save valuable time with pre-built image scanning policies enabling you to quickly catch vulnerabilities, misconfigurations, and more.
- Eliminate threats prior to production: Block exploitable vulnerabilities based on IOAs before runtime, eliminating headaches for security teams.
- Continuously monitor: Identify new vulnerabilities at runtime, alert and take action without having to rescan images.
Automated CI/CD Pipeline Security
- Accelerate delivery: Create verified image policies ensuring only approved images are allowed to progress through your pipeline and run on your hosts or Kubernetes clusters.
- Identify threats earlier: Continuously scan container images for known vulnerabilities, configuration issues, secrets/keys and OSS licensing issues.
- Assess the vulnerability posture of your pipeline: Uncover hidden malware present in the downloaded base images before containers are deployed.
- Improve security operations: Streamline visibility for security operations by providing insights and context for misconfigurations and compliance violations.
- Integrate with developer toolchains: Seamlessly integrate with Jenkins, Bamboo, GitLab and more, to remediate and respond faster within existing DevOps toolchains.
- Enable DevSecOps: Reporting and dashboards drive alignment and a shared understanding across security operations, DevOps and infrastructure teams.
Runtime Protection
Protect running containers wherever they reside.
- Secure hosts and containers: CrowdStrike Falcon® runtime protection defends containers and Kubernetes against active attacks.
- Gain broad container support: Falcon supports containers running on Linux and is deployable across Kubernetes environments such as EKS. It also supports container as a service (CaaS) such as Fargate, providing the same level of protection. Technology previews are available for AKS, GKE and Red Hat OpenShift.
- Leverage market-leading protection technologies: Machine learning (ML), artificial intelligence (AI), IOAs and custom hash blocking automatically defend against malware and sophisticated threats targeting containers.
- ML and AI: Falcon leverages ML and AI to detect known and unknown malware within containers without requiring scanning or signatures.
- IOAs: Falcon uses IOAs to identify threats based on behavior. Understanding the sequences of behavior allows Falcon to stop attacks that go beyond malware, including fileless attacks.
- Stop malicious behavior: Behavioral profiling enables you to block activities that violate policy, with zero impact to legitimate container operation.
- Detect rogue containers: Maintain an up-to-date inventory as containers are deployed and decommissioned, detect and scan rogue images, and identify and stop containers launched as privileged or writable.
- Container drift prevention: Enforce container immutability by detecting new binaries created and executed inside containers.
- Investigate container incidents faster: Easily investigate incidents when detections are associated with the specific container and not bundled with the host events.
- See everything: Capture container start, stop, image and runtime information, and all events generated inside the container, even if it only runs for a few seconds.
- Deploy seamlessly with Kubernetes: Deploy easily at scale by including it as part of a Kubernetes cluster.
- Improve container orchestration: Capture Kubernetes namespace, pod metadata, process, file and network events.
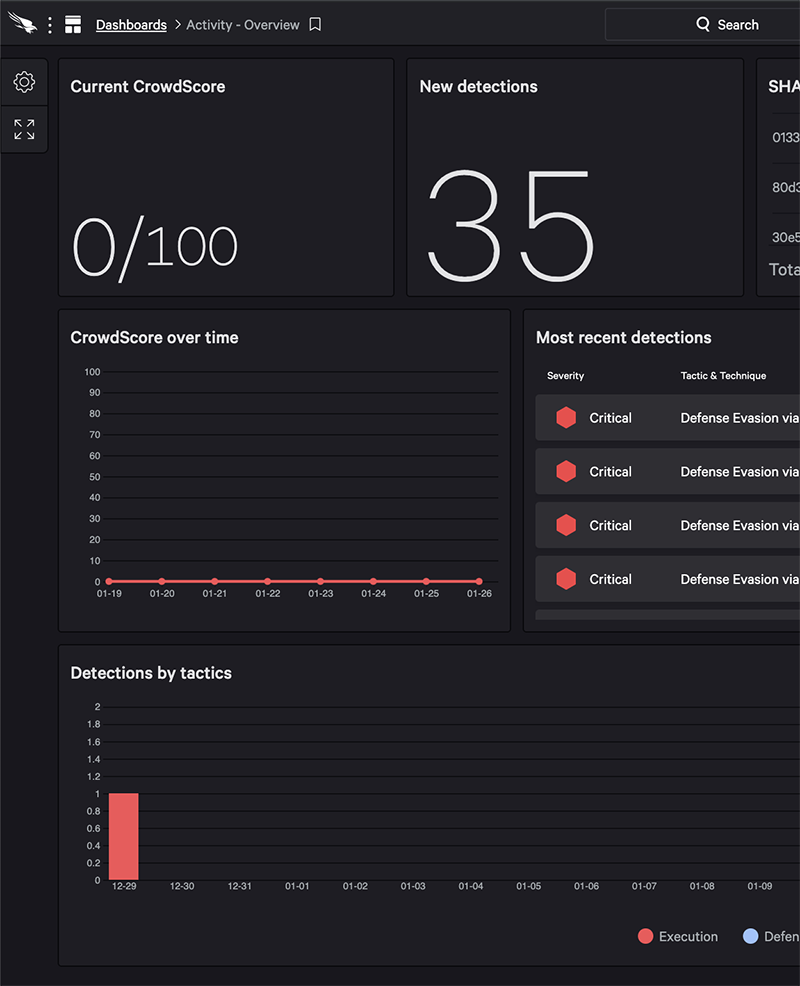
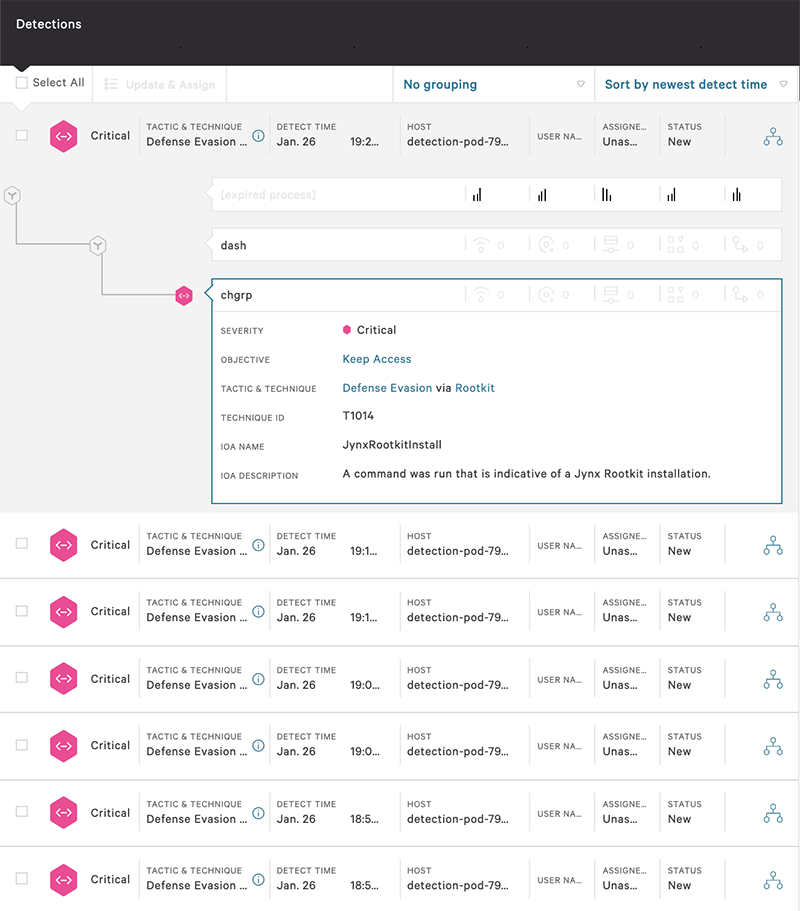
Incident Response and Forensics for Workloads and Containers
- Real-time visibility: Stream container information and activity to the Falcon platform in real time for in-depth insight, enabling security teams to uncover hidden threats, hunt and investigate.
- Powerful search: Filter events inside containers from the worker node and search based on container metadata such as images, mode, configuration type and more.
- Proactive threat hunting: Once deployed, Falcon records container details and activity, enabling proactive threat hunting where security teams can hunt, get query results in seconds and easily pivot from one clue to the next.
- Continuous availability: Event details provide forensic evidence and a full set of enriched data, even for ephemeral containers after they have been decommissioned.
- Ability to unravel entire attacks on one screen: An easy-to-read process tree provides full attack details in context for faster and easier investigations.
Simplicity and Performance
- Simplifies DevSecOps adoption: Reduces the overhead, friction and complexity associated with protecting cloud workloads, containers, and serverless environments.
- Single-pane of glass: One console provides central visibility over cloud security posture, workloads, and containers regardless of their location.
- Complete policy flexibility: Apply at individual workload, container, group or higher level and unify policies across both on-premises and multi-cloud deployments.
- Scales at will: No rearchitecting or additional infrastructure required.
- Gain broad platform support: The Falcon platform supports Open Container Initiative (OCI)-based containers such as Docker and Kubernetes and also self-managed and hosted orchestration platforms such as GKE (Google Kubernetes Engine), EKS (Amazon Elastic Kubernetes Service), ECS (Amazon Elastic Container Service), AKS (Azure Kubernetes Service) and OpenShift.
Cloud Integrations
Optimize your investments and get started faster

Cloud Workload Protection:
- AWS Control Tower
- AWS Systems Mgr
- AWS sensor bootstrapping
- Azure extensions(Sensor boot strapping)
- AWS Security Hub: Falcon Integration Gateway
- AWS Network FW Service
- Container Security (EKS, GKE, Fargate)

DevOps & Cloud-Native
- Go Falcon CS GoLang OAuth2 API SDK
- Falcon Py CS Python OAuth2 API SDK
- PS Falcon CS Powershell OAUTH2 API SDK
- Kubectl-Falcon: Plug-in to kubectl command-line tool
- Falcon Helm: Falcon Helm Chart and the Helm Operator are designed to deploy and manage the Falcon sensor
- Falcon Operator: Simplifies building container applications
Documentation:
Download the CrowdStrike Container Security Datasheet (.PDF)

