
CrowdStrike Falcon X Recon
Digital Risk Protection
Falcon X Recon: Digital Risk Protection
CrowdStrike Falcon X Recon monitors potentially malicious activity across the open, deep and dark web to enable organizations to better protect their brand, employees and sensitive data.
Digital Risk Reconnaissance Across the Dark Web and Beyond
CrowdStrike Falcon X Recon exposes potentially malicious activity from the open, deep and dark web, enabling organizations to better protect their brand, employees and sensitive data. Falcon X Recon collects data and monitors activity from millions of restricted web pages, criminal forums and encrypted messaging platforms - the hidden recesses of the internet where criminal actors congregate and underground digital economies thrive. By empowering security teams to conduct investigations in real time, they can proactively uncover fraud, data breaches, phishing campaigns and other online threats that target their organization.
Benefits
Gain situational awareness across the dark web and beyond

Broad Coverage
Falcon X Recon exposes digital risk by monitoring the hidden recesses of the internet where criminal actors congregate and underground economies thrive.
Instant Visibility
Falcon X Recon provides real-time visibility to potential threats, reducing investigation time and improving efficiency and response.

Immediate Impact
Take immediate action against digital risk on Day One - Falcon X Recon is built on the cloud-native CrowdStrike Falcon® Platform so there’s nothing to install, administer or deploy.
Collect
Falcon X Recon provides instant access to over eight years of data from difficult-to-access digital channels of the open, deep and dark web. Falcon X Recon proactively collects raw intelligence about fraudulent activity, stolen data, threats to enterprises, and identified exploits and tools in the adversaries’ arsenals.
- Collect raw intelligence at scale: Automatically monitor data from millions of hidden web pages and thousands of restricted forums, marketplaces, paste sites, IRC channels, rogue apps, phishing domains, and open and closed messaging applications like Telegram, QQ and more.
- Perform real-time, covert investigations: Disrupt adversaries with access to real-time raw intelligence, and limit their opportunities to attack. Perform investigations with undetectable access to data from restricted sites. Falcon X Recon stores historical data so adversaries can’t cover their tracks by changing or deleting posts.
- Track criminal adversaries: Analyze and track attacker behavioral changes over time, and identify increases in activity, emerging attacks, new targets, and evolving tradecraft and tools, so you can better protect against external threats.
Investigate
Gain real-time visibility to potential threats, and accelerate investigations into fraudulent activity targeting your organization. Falcon X Recon eliminates risky guesswork and enriches traditional incident response by providing broader context to improve the depth and breadth of investigative reporting and analysis.
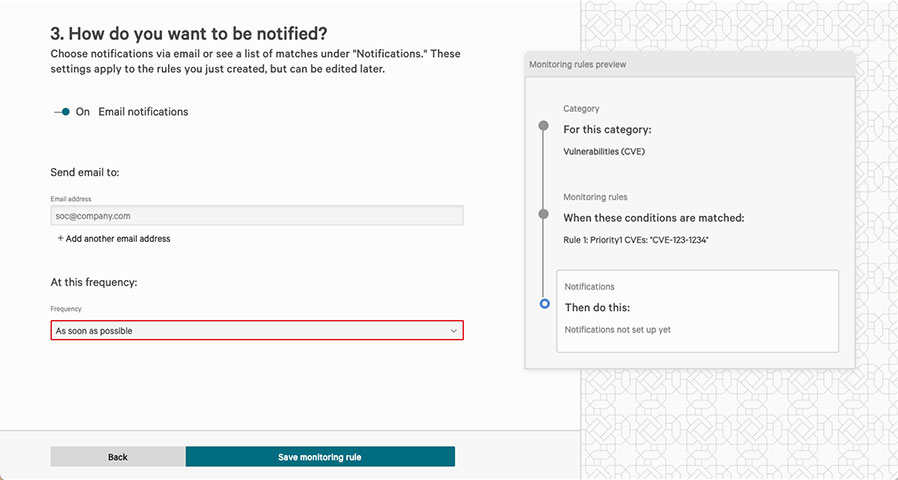
- Identify targeted threats: Continuously monitor underground environments for external threats to the organization without the need for creating complex queries. Falcon X Recon provides easy-to-use wizards that include predefined search criteria, like brand names, executives, domains, vulnerabilities, email addresses and many more. Create and save your own monitoring rules to proactively sift through raw intelligence or share them with your team.
- Expose the adversary: Investigate results displayed in customizable dashboards and easy-to-read cards. Users can view the original threat actor posts with additional context about the actor and the site. Results are viewed in their original language and can be translated from 18 other languages using augmented translation with hacker slang dictionaries.
- Enrich investigations: Gain a complete understanding of the threat. Universal Search enables users to automatically correlate Falcon X Recon results with additional context provided by other licensed CrowdStrike Falcon modules. Maximize efficiency and effectiveness of response by revealing the relationships between digital threats and endpoint detections, hosts, threat intelligence reports, vulnerabilities and much more.
Notify
Optimize the investigation and response workflow with real-time notifications when potential threats are identified. Ensure that the users responsible for triage and response have the details they need at their fingertips.
- Prioritize alerts: Set the priority of the alert based on the criticality of the external threat. Immediately pivot from the notification to the details of the alert.
- Gain complete administrative control: Customize how team members are notified and how often they receive alerts. They can be alerted immediately or on a schedule such as daily or weekly. Toggle notifications on or off without affecting the underlying monitoring rule.
- Inform the right team: Go beyond cybersecurity - digital threats affect an organization’s brand, reputation and employee safety. Alert your departments outside of security, such as marketing, legal, human resources and fraud.
Falcon X Recon Offerings
Choose the option that suits you best

Falcon X Recon
Falcon X Recon enables security teams to monitor and track adversaries across the open, deep and dark web.

Falcon X Recon+
Includes everything in Falcon X Recon, but CrowdStrike manages it for you. Falcon X Recon+ reduces the time, skills and effort required for you to battle sophisticated adversaries.
Falcon X Recon |
Falcon X Recon+ |
|
|---|---|---|
| Access Data from the Open, Deep, and Dark Web | ||
| Create Monitoring Rules | ||
| Set and Manage Alerts | ||
| Universal Search | ||
| Actor Profiles and Indicator Feed | ||
| Assigned CrownStrike Expert |
||
| Managed Rule Monitoring | ||
| Alert Triage and Assessment | ||
| Mitigation Recommendations | ||
| Updates and Threat Briefing | ||
| Takedown Service |
Documentation:
Download the CrowdStrike Falcon X Recon Datasheet (.PDF)

