
CrowdStrike Falcon Horizon Cloud Security Posture Management
Stop cloud breaches in their tracks with unified visibility, threat detection and continuous monitoring and compliance for multi-cloud environments
Falcon Horizon Cloud Security Posture Management (CSPM)
Cloud security posture management that detects and prevents misconfigurations and control plane threats, eliminates blind spots, and ensures compliance, across AWS, Azure, and Google Cloud.
See More, Know More, Do More with Falcon Horizon
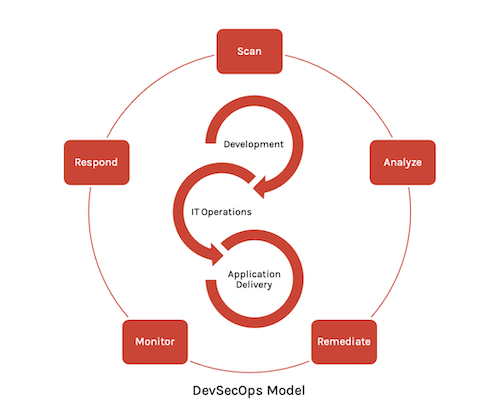
The adoption of the cloud has fundamentally changed how businesses go to market and develop modern applications. Today’s application development lifecycle places a premium on speed to market, requiring development teams to build cloud-native applications supported by a programmable infrastructure that enables businesses to change and reconfigure the cloud infrastructure on the fly.
This shift presents new challenges that make it difficult for security teams to keep up. The result is poor visibility and control of cloud resources, fragmented approaches to detecting and preventing misconfigurations, an increasing number of security incidents and the inability to maintain compliance.
CrowdStrike Falcon Horizon streamlines cloud security posture management across the application development lifecycle for any cloud, enabling you to securely deploy applications in the cloud with greater speed and efficiency. The cloud-native CrowdStrike Falcon platform provides visibility into your entire cloud infrastructure, continuous monitoring for misconfigurations and proactive threat detection - allowing DevSecOps teams to fix issues faster and be more productive.
Key Benefits of Choosing Falcon Horizon

UNIFY VISIBILITY AND SECURITY ENFORCEMENT ACROSS MULTI-CLOUD ENVIRONMENTS
Falcon Horizon delivers continuous discovery and visibility of cloud-native assets from the host to the cloud, providing valuable context and insights into the overall security posture and the actions required to prevent potential security incidents.

PREVENT CLOUD MISCONFIGURATIONS AND ELIMINATE COMPLIANCE VIOLATIONS
Falcon Horizon provides intelligent monitoring of cloud resources to detect misconfigurations, vulnerabilities and security threats, along with guided remediation to resolve security risks and enable developers with guardrails to avoid costly mistakes.

CONTINUOUSLY DETECT AND PREVENT CLOUD CONTROL PLANE AND IDENTITY-BASED THREATS
Falcon Horizon’s adversary-focused approach provides real-time threat intelligence on 150+ adversary groups, 50+ IOA detections and guided remediation that improves investigation speed by up to 88%, enabling teams to respond faster and stop breaches.
Cloud Discovery and Visibility
Unify visibility and security enforcement across multi-cloud and on-premises environments in a single cloud-native solution.
- Single source of truth: Get up and running in minutes and access a single source of truth for all cloud assets and security configurations across multi- cloud environments and accounts.
- See everything: Discover cloud resources and details automatically upon deployment, including misconfigurations, metadata, networking, security, access control and change activity, and eliminate security blind spots.
- Simplified management and security policy enforcement: Manage and enforce security group policies across accounts, projects, regions and virtual networks from a single console to reduce the attack surface.
- Monitor the control plane: Scale at will and gain insight into all control plane API calls and uncover security risks within managed Kubernetes clusters.
- Identify unprotected resources: Identify cloud resources not protected by Falcon and take immediate action.
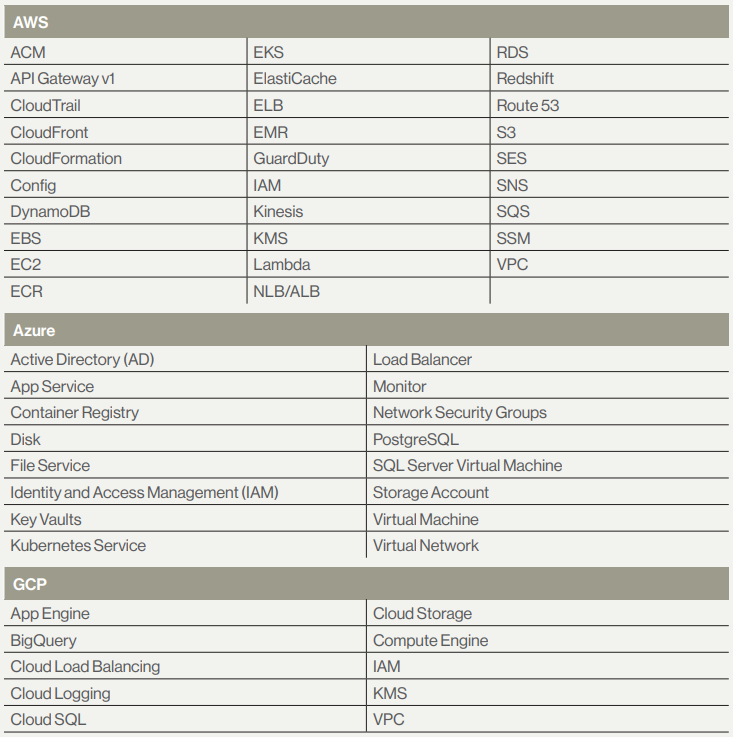
- Supported Services: To see a complete list of all monitored services
Misconfiguration Management & Remediation
Prevent risky cloud misconfigurations based on CrowdStrike best practices.
- Eliminate misconfigurations and compliance violations: Compare cloud application configurations to industry and organizational benchmarks, to identify violations and remediate in real time to ensure application availability.
- Guided remediation from security experts: Find and fix issues that leave cloud resources exposed - such as misconfigurations, open IP ports and unauthorised modifications - with guided remediation and guardrails that enable developers to avoid critical mistakes.
- Enforce permissions: Monitor storage to ensure permissions are secure and not publicly accessible.
- Prevent identity-based threats: Reduces the number of tools required from 3 to 1 and prevent users from putting your organization at risk by automating the detection and remediation of identity-based risks in Azure and AWS.
- Secure Azure AD: Ensure Azure AD groups, users and apps have the correct permissions using the new Identity Analyzer reports.
- Reduce alert fatigue: Remediate issues faster and reduce SOC costs with enhanced policy management for cloud accounts, regions or specific resources.
- Ensure resilience: Monitor database instances and verify that high availability, backups and encryption are enabled, as well as security groups to limit exposure.
Real-Time Threat Detection
Continuously detect, prevent and remediate cloud control plane security threats to stop breaches.
- Accelerate response: Reduce the time it takes to detect and mitigate a breach from months to minutes with an adversary-focused approach that cuts through the noise with 50 out-of-the-box IOA policies designed to stop breaches save time and allow DevSecOps teams to take the most effective action.
- Confidence scoring and prioritization: Falcon Horizon’s patent-pending Confidence Scoring continuously aggregates, assesses and scores control plane threats and configurations to accurately identify malicious activity, reducing the time to understand and respond.
- IOA for cloud with Integrated threat intelligence: Delivers real-time alerting and reporting on 150+ cloud adversaries based on CrowdStrike’s market leading threat intelligence and research, for more effective response.
- Continuous control plane threat detection: Provides ML and behavior-based TTP/IOA detections and guided remediation for all cloud accounts, services and users across the cloud estate and improves investigation speed by up to 88%.
- Self-service threat hunting: Provides cloud-scale data and analytics for all cloud activity, enabling security teams to proactively uncover hidden threats and take action.

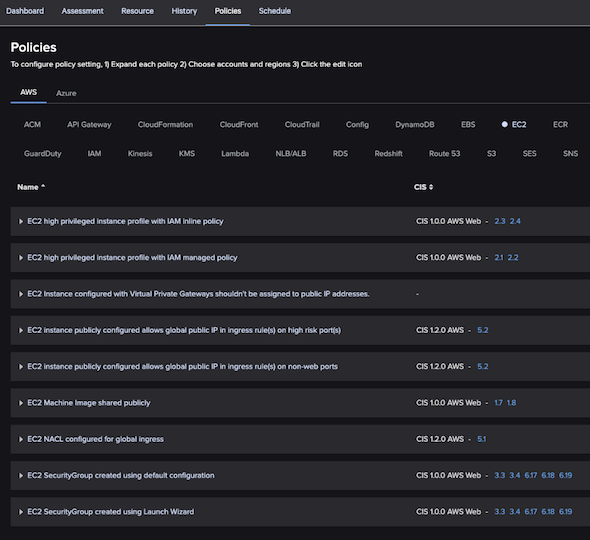
Continuous Compliance Monitoring
Assess the security of cloud accounts and eliminate costly compliance violations.
- Continuous compliance monitoring: Continuously monitor the compliance posture of all of your cloud resources from a single console.
- CIS benchmark assurance: Enables you to assess the security of cloud accounts against Docker and Kubernetes CIS benchmarks with 250 out-of-the-box adversary-focused policies saving time and reducing operational costs.
- Audit-ready compliance: Continuously monitor the compliance of all of your cloud resources and avoid costly fines from a single console for regulations including PCI, NIST and more.
- Eliminate compliance violations: Identify policy violations and take immediate user-driven action to remediate.
Devsecops Integration
Employ cloud-native, agentless posture management to reduce overhead and eliminate friction and complexity across multi-cloud providers and accounts.
- Improve decision making: With SIEM integration, streamline visibility for security operations and provide insights and context into misconfigurations and policy violations for faster incident response.
- Integrate at the speed of DevOps: Using the single API, achieve faster integration and remediation within the DevOps and collaboration tools you already use, such as email, Slack, PagerDuty and more.
- Fuel business performance: Through reporting and dashboards, drive alignment and a shared understanding across security operations, DevOps and infrastructure teams.
Cloud Integrations
Optimize your investments and get started faster

Cloud Security Posture Management
- AWS Control Tower
- AWS - Discover for cloud templates

DevOps & Cloud-Native
- Go Falcon CS GoLang OAuth2 API SDK
- Falcon Py CS Python OAuth2 API SDK
- PS Falcon CS Powershell OAUTH2 API SDK
- Kubectl-Falcon: Plug-in to kubectl command-line tool
- Falcon Helm: Falcon Helm Chart and the Helm Operator are designed to deploy and manage the Falcon sensor
- Falcon Operator: Simplifies building container applications
- AWS Guard Duty
Documentation:
Download the CrowdStrike Falcon Horizon CSPM Datasheet (.PDF)

