
CrowdStrike Falcon Cloud Workload Protection
Workload Protection
Falcon Cloud Workload Protection (CWP)
Comprehensive breach protection for workloads, containers, and Kubernetes enabling organizations to build, run, and secure cloud-native applications with speed and confidence.
Cloud Workload Protection That Transforms The Way Devops Works
The need for speed and agility in today’s digital business requires changes to IT infrastructure, most notably the shift to cloud-native architectures and the adoption of DevOps. This shift has led many businesses to move to containers, microservices and Kubernetes (K8s) to improve the efficiency and scalability of development efforts and form the very foundation for their next-generation, immutable infrastructure.
Additionally, continuous integration/continuous delivery (CI/CD) introduces ongoing automation and continuous monitoring throughout the application lifecycle, from integration and testing to delivery and deployment, resulting in faster innovation. This shift toward CI/CD is not without risk as infrastructure, DevOps and security teams look for ways to ensure containers and microservices remain secure and compliant while eliminating security blind spots.
As containers introduce a new environment and a different management construct with Kubernetes, security teams are finding it difficult to keep up. The result is an increase in risk due to poor visibility; fragmented approaches to detecting and preventing threats; misconfigurations for cloud workloads, containers and serverless; and the inability to maintain compliance.
Common challenges to securing containers include:
- Lack of visibility into cloud workloads, containers and Kubernetes environments
- Ineffective vulnerability management for container images, registries, libraries and hosts
- Securing container orchestration
- Protecting cloud-native workloads and containers at runtime
- Lack of cloud security skills and a growing attack surface
- Meeting and maintaining compliance and enforcing security policies
Manual processes and traditional solutions can’t match the rapid change and unique challenges organizations now face with containers. Alternatives can include complex cloud security platforms or siloed tools, which can add more vendors and increase the complexity of your organization’s overall security.
The CrowdStrike Approach to Securing Cloud Workload and Containers
CrowdStrike secures its cloud infrastructure by focusing on staying ahead of adversaries, relentlessly reducing its attack surface and obtaining total visibility of events taking place in the environment. Stopping breaches across cloud workloads, containers and Kubernetes environments using cloud-scale data and analytics requires a tightly integrated platform. Each function plays a crucial part in identifying vulnerabilities early, detecting threats, protecting at runtime and enforcing compliance, and they must be designed and built for speed, scale and reliability.
CrowdStrike’s experience in operating one of the largest security clouds in the world provides unique insights into adversaries, enabling the delivery of purposebuilt CrowdStrike solutions that create less work for DevSecOps teams, defend against data breaches and optimize cloud deployments.
Key Benefits of Choosing Falcon Cloud Workload Protection
From the host to the cloud and everywhere in between

GAIN COMPLETE VISIBILITY ACROSS YOUR ENTIRE CLOUD ESTATE IN A SINGLE PLATFORM
Falcon Cloud Workload Protection provides complete visibility into workload and container events and instance metadata enabling faster and more accurate detection, response, threat hunting and investigation, to ensure that nothing goes unseen in your cloud environment.

PREVENT ATTACKS AND AVOID BUSINESS DISRUPTION
Falcon Cloud Workload Protection secures your entire cloud-native stack, on any cloud, across all workloads, containers and Kubernetes applications. Automate security and detect and stop suspicious activity, zero-day attacks, risky behavior to stay ahead of threats and reduce the attack surface.

ELIMINATE FRICTION AND STAY SECURE WHILE BUILDING IN THE CLOUD
Falcon Cloud Workload Protection key integrations support continuous integration/continuous delivery (CI/CD) workflows allowing you to secure workloads at the speed of DevOps without sacrificing performance
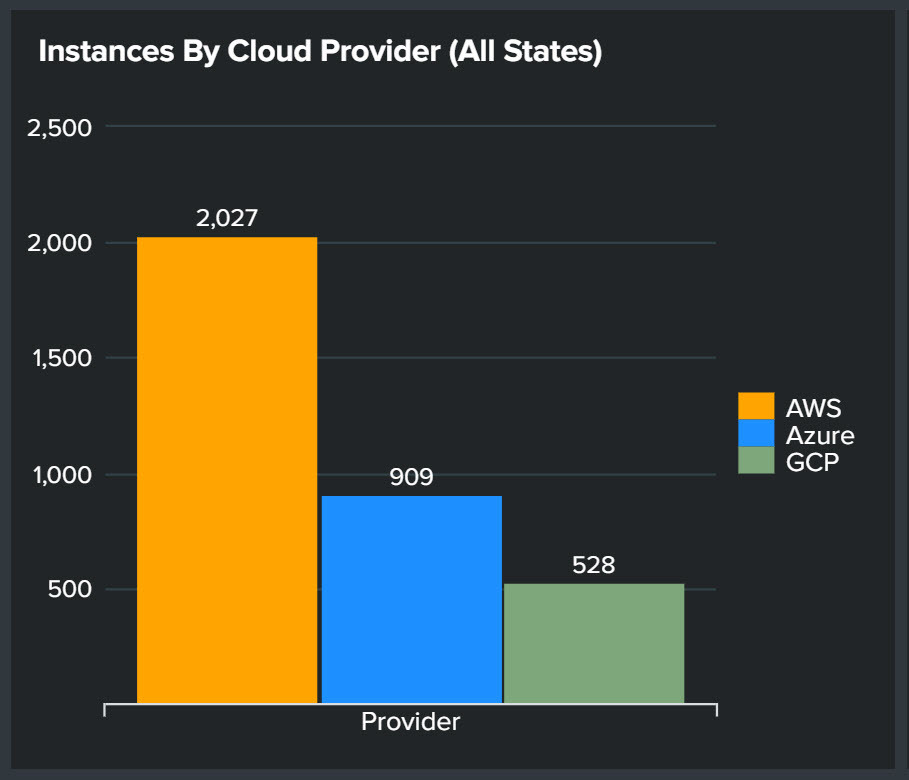
Cloud Platforms
You pick the cloud, CrowdStrike secures it

FALCON FOR AWS

FALCON FOR AZURE

FALCON FOR GCP
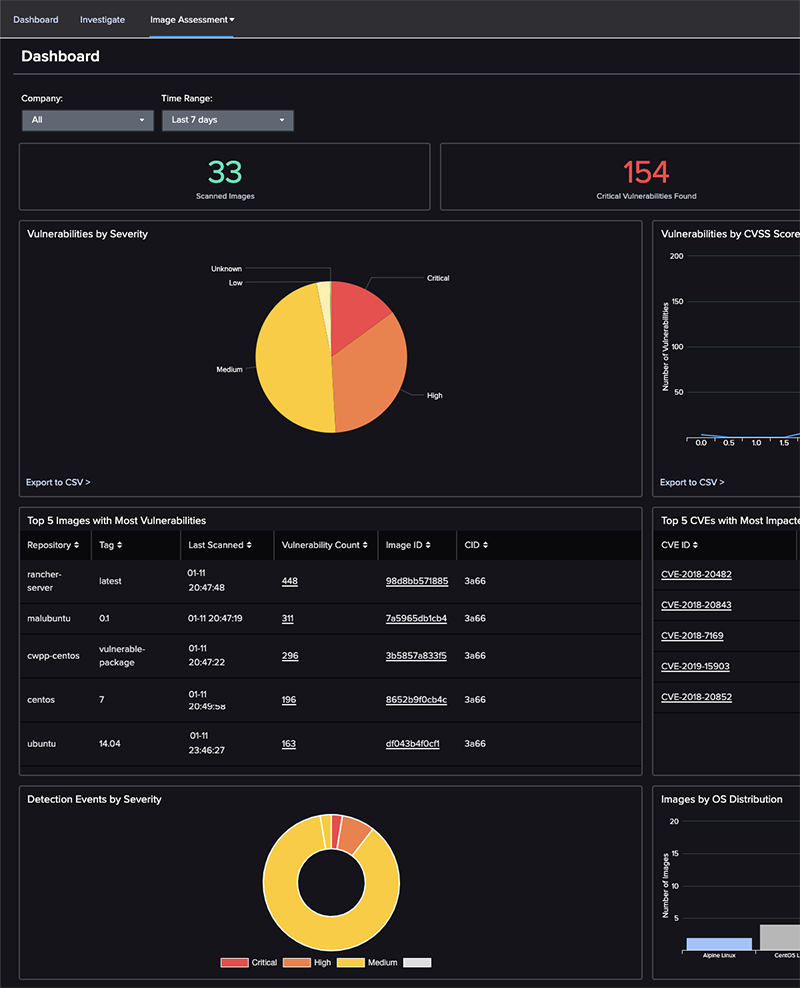
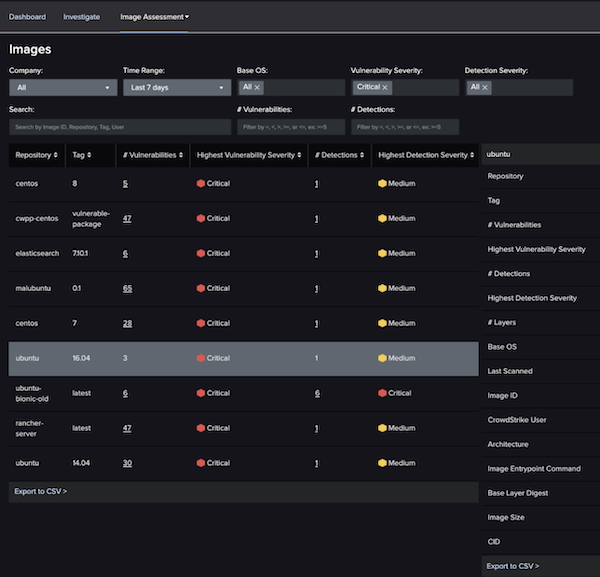
Vulnerability Scanning and Management
- Improve decision making: Gather insights and details about your cloud workload, and container - images, registries, libraries and containers spun from those images.
- Uncover hidden threats: Find hidden malware, embedded secrets, configuration issues and more in your images to help reduce the attack surface.
- Gain visibility into container environments: Get full visibility into running containers to uncover details surrounding file access, network communications and process activity.
- Identify vulnerabilities faster: Save valuable time with pre-built image scanning policies enabling you to quickly catch vulnerabilities, misconfigurations, and more.
- Eliminate threats prior to production: Block exploitable vulnerabilities based on IOAs before runtime, eliminating headaches for security teams.
- Continuously monitor: Identify new vulnerabilities at runtime, alert and take action without having to rescan images.
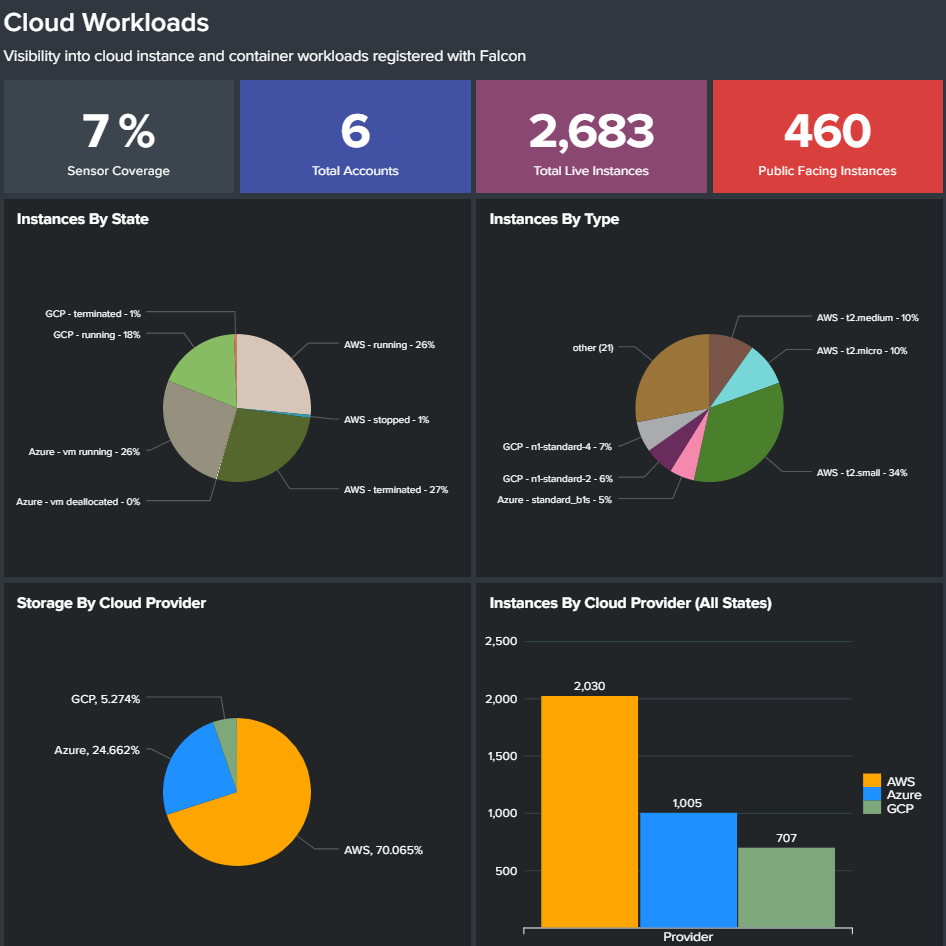
Multi-Cloud Worload Discovery
- Continuous resource discovery: Provides insight into your cloud footprint so you can secure all workloads, uncover and mitigate risks, and reduce the attack surface.
- Automate discovery: Automatically discovers existing cloud workload deployments - without installing an agent - by enumerating AWS EC2 instances, GCP Compute instances, and Azure VMs.
- Granular context and insights: Provides real-time information about workloads including context-rich metadata about system size and configuration, networking, and security group information for AWS, GCP, and Azure.
- Uncover unprotected resources: Identifies workloads that are not protected by the Falcon platform.
Automated CI/CD Pipeline Security
- Accelerate delivery: Create verified image policies to ensure that only approved images are allowed to progress through your pipeline and run in your hosts or Kubernetes clusters.
- Identify threats earlier: Continuously scan container images for known vulnerabilities, configuration issues, secrets/keys, and OSS licensing issues.
- Assess the vulnerability posture of your pipeline: Uncover malware missed by static scanners before containers are deployed.
- Improve security operations: Streamline visibility for security operations by providing insights and context for misconfigurations and compliance violations.
- Integrate with developer toolchains: Seamlessly integrate with Jenkins, Bamboo, GitLab, and more to remediate and respond faster within the DevOps tool sets you already use.
- Enable DevSecOps: Reporting and dashboards drive alignment and a shared understanding across security operations, DevOps and infrastructure teams.

Container Security
- Complete visibility into container environment: Provides complete visibility into container footprint includes on-premises and cloud deployments.
- Prevent attacks on container environments: Uncovers hidden threats in open source packages and 3rd party images, to prevent attacks on your container-based applications.
- Enforce container immutability: Ensures only secure images are allowed to progress through your pipeline and run in your Kubernetes clusters or hosts.
- Log everything: Captures container start, stop, image, runtime information and all events generated inside the container, even if it only runs for a few seconds.
- Easily view container usage: Includes trends and uptime, images used and configuration to identify risky and misconfigured containers.
- Secure hosts and containers: Via a single Falcon agent running on the host, and runtime protection defends containers against active attacks.
- Accelerate investigations: Investigate container incidents easily when detections are associated with the specific container and not bundled with the host events.
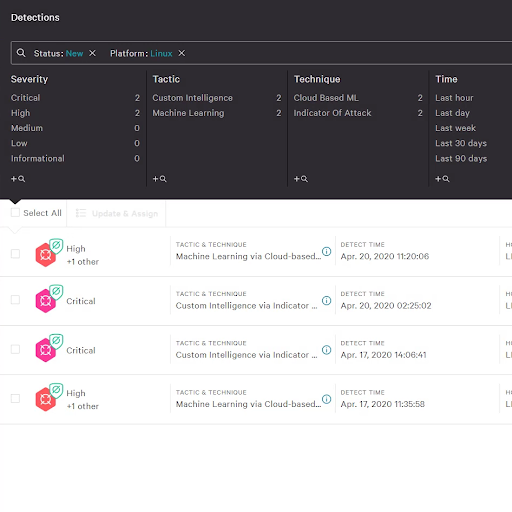
Runtime Protection
- Secure hosts and containers: Falcon runtime protection defends containers against active attacks.
- Broad container support: Supports Linux and Kubernetes environments, such as EKS. Offers container-as-a-service support, including Fargate, providing the same level of protection. Technology previews available for AKS, GKE and Red Hat OpenShift.
- Leverage market-leading protection technologies: Machine learning (ML), artificial intelligence (AI), indicators of attack (IOAs) and custom hash blocking automatically defend against malware and sophisticated threats targeting containers.
- Stop malicious behavior: Behavioral profiling enables you to block activities that violate policy with zero impact to legitimate container operation.
- Investigate container incidents faster: Easily investigate incidents when detections are associated with the specific container and not bundled with the host events.
- See everything: Capture container start, stop, image, runtime information and all events generated inside the container, even if it only runs for a few seconds.
- Deploy seamlessly with Kubernetes: Deploy easily at scale by including it as part of Kubernetes cluster.
- Improve container orchestration: Capture Kubernetes namespace, pod meta data, process, file and network events.

Single Source of Truth with Powerful APIs
- Single data source: Enables security teams with fast access to everything they need to respond and investigate.
- DevOps-ready Automation: Powerful APIs allow automation of CrowdStrike Falcon functionality, including detection, management, response and intelligence.
- Optimize business performance: Unlock security orchestration, automation and other advanced workflows to optimize business performance.
- Integrate with CI/CD pipelines: Chef, Puppet and AWS Terraform integrations support CI/CD workflows.
- Protection at the speed of DevOps: Falcon protects immediately and matches the speed of DevOps, adapting to the dynamic scalability of containers in real time with CI/CD integration via API and pre-boot scripts.
Threat Graph Breach Prevention Engine
- Predict and prevent modern threats: Ensures real-time protection via CrowdStrike Threat Graph®, the industry's most comprehensive sets of endpoint and workload telemetry, threat intelligence and AI-powered analytics.
- Access enriched threat intelligence: Delivers a visual representation of relationships across account roles, workloads and APIs to provide deeper context for faster more effective response.
- Deep AI and behavioral analysis: Identify new and unusual threats in real time and take the appropriate action, saving security teams valuable time.
- Accelerate response: Arms your responders in real time via Threat Graph, empowering them to understand threats immediately and act decisively.
- Targeted threat identification and management: Cuts through the noise of multi-cloud environment security alerts reducing alert fatigue.

MDR for the Cloud
The first and only fully-managed CWP solution, delivering 24/7 expert security management, threat hunting, monitoring, and response for cloud workloads, backed by CrowdStrike’s industry-leading Breach Prevention Warranty.
- 24/7 Expertise to Defend the Cloud: Arms you with seasoned security professionals who have experience in cloud defense, incident handling and response, forensics, SOC analysis and IT administration
- Continuous Human Threat Hunting: Includes 24/7 monitoring by the Falcon OverWatch team, CrowdStrike's human threat detection engine that hunts relentlessly to see and stop the most sophisticated hidden threats.
- Surgical Remediation: The team remotely accesses the affected system to surgically remove persistence mechanisms, stop active processes, clear other latent artifact, and restores workloads to their pre-intrusion state without the burden and disruption of reimaging.
- Breach Prevention Warranty: CrowdStrike stands strongly behind its breach protection capabilities by providing a Breach Prevention Warranty* to cover costs should a breach occur within the protected environment.
Simplicity and Performance
- Simplifies DevSecOps adoption: Reduces the overhead, friction and complexity associated with protecting cloud workloads, containers, and serverless environments.
- Single-pane of glass: One console provides central visibility over cloud security posture, workloads, and containers regardless of their location.
- Complete policy flexibility: Apply at individual workload, container, group or higher level and unify policies across both on-premises and multi-cloud deployments.
- Scales at will: No rearchitecting or additional infrastructure required.
- Broad platform support: The Falcon platform supports Open Container Initiative (OCI)-based containers such as Docker and Kubernetes and also self-managed and hosted orchestration platforms such as GKE (Google Kubernetes Engine), EKS (Amazon Elastic Kubernetes Service), ECS (Amazon Elastic Container Service), AKS (Azure Kubernetes Service) and OpenShift.
Cloud Integrations
Optimize your investments and get started faster

Cloud Workload Protection:
- AWS Control Tower
- AWS Systems Mgr
- AWS sensor bootstrapping
- Azure extensions(Sensor boot strapping)
- AWS Security Hub: Falcon Integration Gateway
- AWS Network FW Service
- Container Security (EKS, GKE, Fargate)

DevOps & Cloud-Native
- Go Falcon CS GoLang OAuth2 API SDK
- Falcon Py CS Python OAuth2 API SDK
- PS Falcon CS Powershell OAUTH2 API SDK
- Kubectl-Falcon: Plug-in to kubectl command-line tool
- Falcon Helm: Falcon Helm Chart and the Helm Operator are designed to deploy and manage the Falcon sensor
- Falcon Operator: Simplifies building container applications
- AWS Guard Duty
Documentation:
Download the CrowdStrike Falcon Cloud Workload Protection Complete Datasheet (.PDF)

